COMP90007, Internet Technologies Practice Exam
Hello, dear friend, you can consult us at any time if you have any questions, add WeChat: daixieit
COMP90007, Internet Technologies Practice Exam
Semester 2, 2021
• This examination is worth of 60% ofyour final mark. It is a 3 hour exam with
15 minutes of reading time.
• There are 19 questions in the exam and a total of4 pages including this cover page.
• You may access other materials during the exam, but you must answer all questions in your own words. Marks will be deducted for non-original answers.
• Attempt all questions, partial marks will be available. No question requires writing lengthy answers. Please be clear and brief as you may lose points for unclear or redundant descriptions.
• The values in square brackets after questions show the marks allocated to each question.
• You are welcome to use the text editor or word processor ofyour choice to type your answers. Do not need to repeat the questions in your answers; just make sure you use the right question number per answer.
• Type your answers: No handwritten answers.
• Start your answer document with writing your student ID on top ofyour document, e.g., “Student ID: …”. Then please mention “COMP90007 Final Exam Answers” in the next line. Then go to the next next line and start with your answers as: “Question 1 Answer: …” and so on.
• Please answer questions in the given order and separate the answers with a few blank lines to give some space between the answers to different questions.
• Make sure to save your progress locally during the exam and at the end a PDF version ofyour file too. Upload only that PDF version when you are finished. We recommend not leaving the uploading ofyour PDF version to the last minute.
Question 1 [4 marks]
Briefly explain key advantages and disadvantages of using Fibre Optics versus Copper Wire.
Question 2 [4 marks]
(1) How can you increase the bit rate of a 1200KHz line from X bit/s to 3X bit/s without changing the frequency?
(2) Consider a telephone line that is bandwidth limited to 4kHz. If we use 32 levels, what is the bit rate achieved to transmit data?
Question 3 [2 marks]
(1) The following data fragment occurs in the middle of a data stream for which the byte-stuffing algorithm described in the lectures is to be applied:
A B ESC D FLAG FLAG ESC C
Show the output data stream after the byte-stuffing algorithm has been applied.
(2) What is the maximum overhead in the byte-stuffing algorithm in general and when does it occur?
Question 4 [2 marks]
Briefly explain the difference in operation and philosophy of two approaches to error handling on the data link layer, error-correcting and error-detecting.
Question 5 [2 marks]
If a LAN is under high load, would it be more efficient to use a contention protocol or a collision free protocol in the MAC sublayer? Briefly explain your answer.
Question 6 [3 marks]
Give the name of one sliding window protocols and briefly explain how that protocol works at Data Link Layer when a transmission error occurs.
Question 7 [4 marks]
A router has built the following routing table. The router can directly deliver packets over Interface 0 and Interface 1 or it can forward to routers R2, R3 and R4.
|
Start |
Subnet Mask |
Next Hop |
|
148.96.39.0 |
255.255.255.0 |
Interface 0 |
|
148.96.39.128 |
255.255.255.128 |
Interface 1 |
|
148.96.40.0 |
255.255.255.128 |
R2 |
|
196.4.153.0 |
255.255.255.192 |
R3 |
|
default |
|
R4 |
Describe what the router does if a packet addressed to each of the following destinations is received.
Question 8 [2 marks]
What are the main purposes of subnetting? Briefly explain your answer.
Question 9 [4 marks]
With respect to routing packets in the Network Layer, explain the difference between a connectionless and connection-oriented service?
Question 10 [6 marks]
Distance vector routing is used for a network of six nodes as shown below.
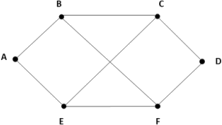
The following vectors have just come into router C from B: (5, 0, 7, 11, 10, 7); from D: (15, 11, 4, 0, 10, 11); and from E: (5, 10, 6, 10, 0, 3). Each vector contains the distances from a certain node to the other nodes, in the order of (A, B, C, D, E, F). The distances from C to B, D, and E, are 7, 4, and 6, respectively.
What is the new vector for C? Show a table ofthe outgoing lines to use and the expected distances from C to all the other nodes.
Question 11 [3 marks]
A common approach to removing jitter in streaming audio is to buffer incoming packets at the receiver. Briefly explain a key problem using this approach for video conferencing.
Question 12 [2 marks]
Name two services that DNS provides.
Question 13 [3 marks]
An encrypted file needs to be accessed in non-sequential order. Which cipher mode is best suited to encrypting this file, and briefly explain why.
Question 14 [4 marks]
What are Symmetric and Asymmetric key algorithms? Briefly explain while highlighting differences between these two categories.
Question 15 [4 marks]
Consider a client program that needs to run the following operations on a remote file server:
a. List the contents of a directory
b. Open a file
c. Read a text file
d. Display the attributes of a file
For each of the above operations, indicate whether they are more likely to be delay sensitive or bandwidth sensitive. Justify your answer?
Question 16 [3 marks]
Give an example of application that has stringent requirements on each ofthe three main characteristics: Bandwidth, Latency, Jitter.
Question 17 [2 marks]
Does email application use the DNS protocol? If yes, how?
Question 18 [4 marks]
What is the man-in-the-middle attack problem in authentication?
Question 19 [2 marks]
Given an example of symmetric and asymmetric key generation protocols in network security.
2021-12-10