COMP2410/COMP6340_Semester 1 Networked Information Systems Semester 1 - Final exam, 2019
Hello, dear friend, you can consult us at any time if you have any questions, add WeChat: daixieit
EXAMINATION
Semester 1 - Final exam, 2019
COMP2410/COMP6340_Semester 1 Networked Information Systems
SECTION A.
Format each answer as a 400-600-word essay. You are encouraged to include figures and tables to support your free-form text answer. Remember to demonstrate your academic communication skills.
1. [25 marks; 25% total]
Define both symmetric and asymmetric encryption. Give examples of these encryption approaches when used by VeraCrypt for email communication. Would using VeraCrypt to email your thesis manuscript as an attachment to your thesis examiner be an example of symmetric encryption, asymmetric encryption, or both? Remember to include a justification of your answer and enrich your essay by encryption flowcharts.
2. [25 marks; 25% total]
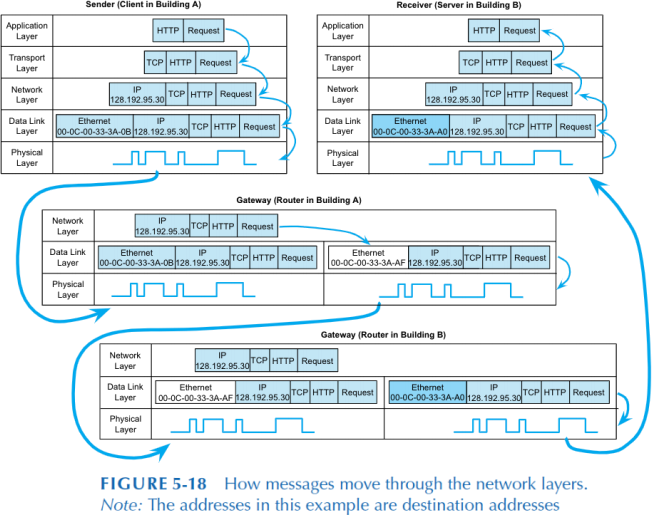
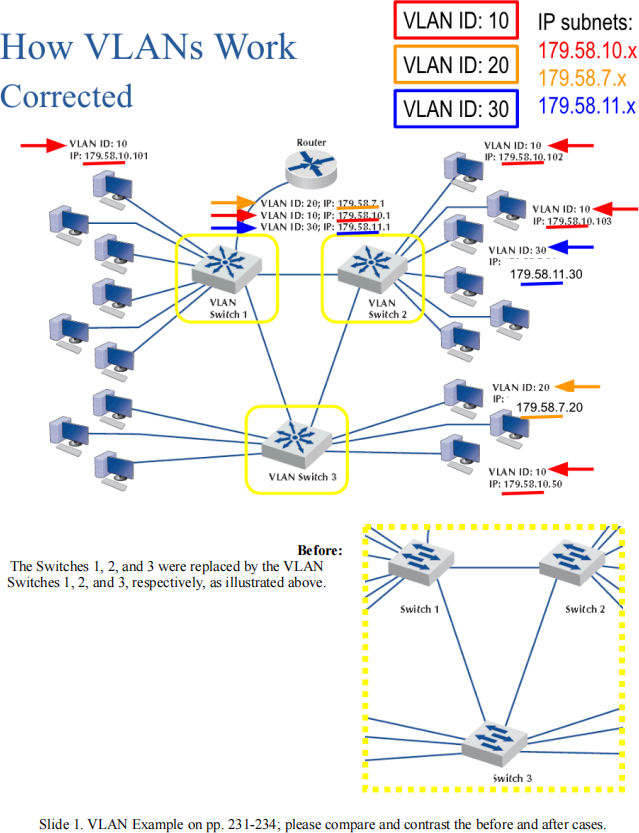
First, define routers, virtual local area network switches, and layer-2 switches. Then, compare and contrast these devices in the context of Figure 5- 18 and Slide 1 below from the textbook (FitzGerald J, Dennis A, Durcikova A (2014) . Business Data Communications and Networking, 12th Edition. Wiley). In particular, please relate the concept of device transparency to these figures.
SECTION B.
3. [30 marks; 30% total]
Answer the following question. Format your answer as a max 1-page table in your answer booklet.
During the 2019 Semester 1, a range of networked information systems/technologies have been used to support the COMP2410/COMP6340 lectures, including, but not limited to, the following examples: Wattle, Piazza, Google Drive (e.g., Slides, Forms, and folders of PDF documents), YouTube, Poll Everywhere, TinyURL, Smartphone, PC, and Wi-Fi/Access
Points.
Remembering to demonstrate your mastery of a wide range of security threats and controls, please compare and contrast these systems/technologies by copying and populating the following table in your answer booklet:
|
|
What was this system/technology used for? |
Why is this a networked system/ technology? |
Identify and justify a major security threat in this context |
Identify and justify a security control to manage this major threat |
|
Wattle |
|
|
|
|
|
Piazza |
|
|
|
|
|
Poll Everywhere |
|
|
|
|
|
Wi-Fi/Access Points |
|
|
|
|
SECTION C.
4. [20 marks; 20% total]
Answer the following 10 multiple-choice questions. Format your full answer as a list of the following kind in your answer booklet:
1. A, B
2. B
3. C, D
…
10. A, B, E
Please note that A, B, C, … illustrate the answer format (and not the right answers) above. For each question, 2 marks are given if the answer is 100% correct, 1.2 marks are given if it is almost correct (typically 1 or 2 differences), and 0 marks are given otherwise.
1. Which statement or statements are correct?
A. A metropolitan area network (MAN) connects one or more wide area networks (WANs).
B. A backbone network (BN) connects one or more WANs.
C. A BN connects one or more local area networks (LANs).
D. A LAN connects one or more BNs.
E. A WAN spans hundreds or thousands of miles.
F. Typically BNs use leased lines from interexchange carriers.
2. Which statement or statements are correct?
A. In BNs, improving circuit capacity is a way to improve performance.
B. In BNs, increasing device performance is a way to improve performance.
C. In BNs, changing circuits from gigabit Ethernet to 100Base-T Ethernet is a way to improve performance.
D. In BNs, reducing network demand is a way to improve performance.
E. Using data compression techniques for all data in the network is a way to reduce network demand.
F. Moving data further from the applications and people who use them is a way to reduce network demand.
G. Shifting network usage from high cost times to lower cost times is a way to reduce network demand.
H. Requiring a network impact statement for all application software developed by the organisation is a way to reduce network demand.
3. Which network design claim or claims are true?
A. In designing BNs, network designers tend to err on the side of providing for more capacity than what is currently necessary.
B. In designing MANs, network designers tend to err on the side of providing for less capacity than what is currently necessary.
C. In designing LANs, network designers tend to err on the side of providing for more capacity than what is currently necessary.
D. In designing WANs, network designers tend to err on the side of providing for more capacity than what is currently necessary.
E. In designing LANs, network designers tend to err on the side of providing for less capacity than what is currently necessary.
4. Which topology or topologies belong to the basic architectures of dedicated-circuit networks?
A. Mesh.
B. Ring.
C. Square.
D. Star.
E. Triangle.
F. Web.
5. Which reason or reasons forbid the use of applications based on the peer-to-peer architecture in most organisations including theANU?
A. The sensitivity of the information shared in peer-to-peer networks, such as copyright material.
B. Hosting of information on the organisation’s computers raises responsibility for the organisation.
C. Users may access peer-to-peer to download material for entertainment.
D. Users may access peer-to-peer to download illegal contents.
E. Users may be exposed to distressing contents by accessing peer-to-peer.
F. The security of the whole organisation’s network can be compromised due to hosting of insecure software.
G. The use of network facilities for purposes that are beyond the organisation’s
concern.
6. Which term or terms refer to the use of computer analysis techniques to gather evidencefor criminal and/or civil trials?
A. Misuse detection.
B. Tunnelling.
C. Computer forensics.
D. Sniffing.
E. Deception.
7. Which definition or definitions explain the term of IP spoofing?
A. To illegally tape or listen in on telephone conversations.
B. To act as an intermediate host computer between the Internet and the rest of the organisation’s networks.
C. To clad or cover the internal processing (IP) lines with insulating material to shield the IP lines from excess heat or radiation.
D. To fool the target computer and any intervening firewall into believing that messages from the intruder’s computer are actually coming from an authorised user inside the organisation’s network by utilising the Internet protocol (IP) addressing.
8. Which category or categories can be used to characterise distributed denial-of- service agents?
A. Trojans.
B. Phishing emails.
C. Intrusion prevention and detection approaches.
D. Deception intelligence.
9. Which risk assessment claims are true?
A. Controls that have been implemented and will be implemented should not be included in risk assessment.
B. A risk assessment should be simple so that both technical and non-technical readers can understand it.
C. After reading a risk assessment, anyone should be able to see which systems and network components are at high risk for attack.
D. Risk assessment frameworks are used to provide strategies for analysing and prioritising the security risks to information systems and networks.
10. Which claims about one-time passwords are true?
A. They can be used in conjunction with a token system.
B. This is a good security solution for users who travel frequently and who must have secure dial-in access.
C. They create a packet level firewall on the system.
D. The user must enter the one-time password to gain access or the connection is terminated.
2023-06-20